What’s wrong with Passkeys advocacy?
Published Nov 2, 2023
The “quest to replace passwords” is already several decades old. I mean the intention, not the now classic research paper of the same title by Joseph Bonneau et al from 2012. (¹)
Frustratingly, the security pop culture keeps ignoring the elephant
in the room — the elephant academic researchers are pretty well
aware of. Namely: there is no such thing as a password you can blame and sacrifice for the user’s sins. Not anymore. And whatever exists, it is not something with consistent security properties, not on the web at least.
Passwords are not inherently BAD, and they are not exactly “passwords”.
There are TWO things.
1. The “password” itself. The term “password” is misleading and might be better if replaced by something entirely different. Not the password, just the word. Think about it as “shared exportable secret”, or whatever.
Not great, not terrible. It has some inherent specifics that could make it not the best choice, but it is not even close to true abominations like “security questions” or SMS codes.
2. The authentication framework that supports the secret life cycle: generation, use, cross-device sync, recovery, and revocation.
And, man, the second part is complex and volatile.
The earliest and ugliest version is “human” implementation where authentic human brains are used to generate and store secrets and also to manage access so it won’t be revealed to untrusted parties. Neither of these ever worked well, and that’s what security evangelists typically use to tell us the scary tales.
There is a human being to blame, and it could be and should be removed from the process.
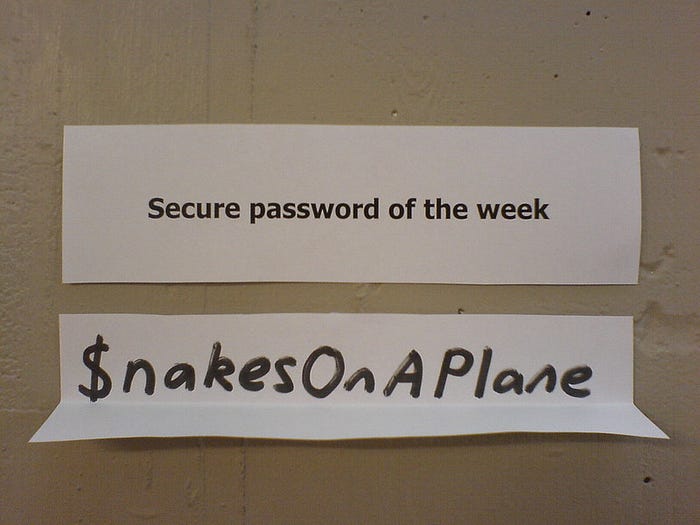
Image credit: Simon Lieschke
- Humans are terrible as an entropy source (creating passwords)
- Humans are highly unreliable storage devices (remembering passwords)
- Humans fail to authenticate peers when disclosing secrets (phishing)
Here comes the fix: the “password manager”.
A good password manager should do its work transparently for users with zero friction, which is hardly possible on diverse ecosystems (²) (³). The closest thing to the platonic idea of a good password is probably the MacOS keychain with its system-wide support, as long as we are willing to turn a blind eye to certain implementation specifics, invisible to users (⁴). Despite browser vendors’ direct sabotage (⁵), it works on MacOS Sonoma (⁶), even for Chrome. You would need an “extension”, but most Chrome users are no strangers to extensions. For those who chose Windows Chrome / Android ecosystem things are even easier.
Webauthn is still better, even its questionable (⁷) spinoff Passkeys
Unlike Webauthn / Passkeys, even managed passwords are still not foolproof enough.
A persistent idiot may find his password and copy it manually to a phishing site. A creative control freak can override password generation settings and type in a “favorite” password instead. Web sites still reinforce antipatterns by asking you to “choose a strong password” satisfying “complexity rules” instead of asking you to generate a password and assessing its entropy.
The password UX flow is gradually improving, but it cannot beat modern authentication methods. Its only real advantage is 100% backward compatibility.
PLEASE stop fighting a straw man.
Thus said, I see Passkeys “evangelism” based on the idea Passkeys “liberate you from memorizing complex passwords” (⁸) misleading and totally inappropriate. Webauthn is already better than any other authentication method in almost every possible aspect. It deserves to win in a fair competition.
[1] https://ieeexplore.ieee.org/document/6234436
This paper lays foundational criteria for evaluating authentication methods — everyone now uses something more or less similar.
[2]https://web.archive.org/web/20220307220332/https://userlab.utk.edu/files/papers/oesch2022observational.pdf Sean Oesch et al, “It Basically Started Using Me:” An Observational Study of Password Manager Usage.
[3]https://www.usenix.org/system/files/sec22-mayer.pdf Peter Mayer et al, Why Users (Don’t) Use Password Managers at a Large Educational Institution
[4] The Keychain framework could, in theory, provide amazingly secure hardware-backed password storage with granular per-app, per-secret access authorization. It did not. You can dump all the passwords into a text file with zero effort, and any malicious piece of code can do the same. Unfortunately, this margin is too narrow to contain an in-depth explanation of what went wrong and how it could be avoided.
[5] https://bugzilla.mozilla.org/show_bug.cgi?id=106400#c130 , https://bugs.chromium.org/p/chromium/issues/detail?id=466638
[6] https://twitter.com/rmondello/status/1679204849416835073
[7] https://medium.com/@arkenoi/what-is-wrong-with-apple-passkeys-1d044072c5a3
[8] https://twitter.com/royalhansen/status/1718276382873239573